Which Of These Would Not Be A Filtering Mechanism Found In A Firewall Acl Rule?
Access Rules
This chapter describes how to command network access through or to the ASA using access rules. Y'all utilize access rules to control network access in both routed and transparent firewall modes. In transparent mode, you can use both access rules (for Layer 3 traffic) and EtherType rules (for Layer 2 traffic).
 Note | To admission the ASA interface for direction access, you practise not also need an access dominion allowing the host IP accost. You simply need to configure direction access co-ordinate to the full general operations configuration guide. |
Controlling Network Access
Access rules determine which traffic is immune through the ASA. There are several different layers of rules that work together to implement your access command policy:
-
Extended access rules (Layer 3+ traffic) assigned to interfaces—You can apply split rule sets (ACLs) in the inbound and outbound directions. An extended access rule permits or denies traffic based on the source and destination traffic criteria.
-
Extended access rules (Layer 3+ traffic) assigned to Bridge Virtual Interfaces (BVI; routed mode)—If y'all name a BVI, you tin can apply split up rule sets in the inbound and outbound direction, and yous tin can also apply rule sets to the bridge group member interfaces. When both the BVI and member interface accept admission rules, the order of processing depends on direction. Inbound, the member access rules are evaluated first, then the BVI access rules. Outbound, the BVI rules are considered first, then the member interface rules.
-
Extended access rules assigned globally—Yous can create a single global dominion set, which serves as your default access control. The global rules are applied after interface rules.
-
Management access rules (Layer iii+ traffic)—You can employ a single rule set to cover traffic directed at an interface, which would typically exist management traffic. In the CLI, these are "control plane" access groups. For ICMP traffic directed at the device, you lot can alternatively configure ICMP rules.
-
EtherType rules (Layer 2 traffic) assigned to interfaces (span group member interfaces only)—You can apply carve up rule sets in the inbound and outbound directions. EtherType rules control network access for non-IP traffic. An EtherType rule permits or denies traffic based on the EtherType. You lot can likewise apply extended admission rules to span group member interfaces to control Layer iii+ traffic.
General Information About Rules
The post-obit topics provide general information about admission rules and EtherType rules.
Interface Access Rules and Global Access Rules
You can apply an admission dominion to a specific interface, or you can apply an access rule globally to all interfaces. You can configure global access rules in conjunction with interface access rules, in which case, the specific entering interface access rules are always processed earlier the general global access rules. Global admission rules apply only to entering traffic.
Inbound and Outbound Rules
Yous tin can configure access rules based on the direction of traffic:
-
Inbound—Entering access rules apply to traffic as information technology enters an interface. Global and management access rules are always inbound.
-
Outbound—Outbound rules employ to traffic every bit it exits an interface.
 Note | "Entering" and "outbound" refer to the awarding of an ACL on an interface, either to traffic entering the ASA on an interface or traffic exiting the ASA on an interface. These terms do not refer to the move of traffic from a lower security interface to a higher security interface, ordinarily known as inbound, or from a higher to lower interface, commonly known equally outbound. |
An outbound ACL is useful, for instance, if you want to allow simply certain hosts on the inside networks to access a spider web server on the outside network. Rather than creating multiple entering ACLs to restrict access, you can create a single outbound ACL that allows only the specified hosts. (See the following figure.) The outbound ACL prevents any other hosts from reaching the outside network.
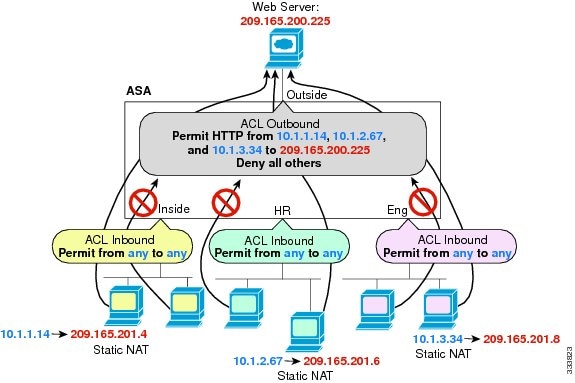
See the following commands for this example:
hostname(config)# access-list OUTSIDE extended permit tcp host 10.1.1.fourteen host 209.165.200.225 eq world wide web hostname(config)# access-listing Outside extended permit tcp host 10.1.2.67 host 209.165.200.225 eq www hostname(config)# access-list Outside extended permit tcp host 10.one.3.34 host 209.165.200.225 eq www hostname(config)# admission-group OUTSIDE out interface outside Rule Order
The gild of rules is important. When the ASA decides whether to forwards or drop a bundle, the ASA tests the parcel against each rule in the order in which the rules are listed in the applied ACL. Afterwards a lucifer is found, no more rules are checked. For example, if you create an access dominion at the beginning that explicitly permits all traffic for an interface, no further rules are always checked.
Implicit Permits
Unicast IPv4 and IPv6 traffic from a college security interface to a lower security interface is allowed through past default. This includes traffic betwixt standard routed interfaces and Span Virtual Interfaces (BVI) in routed mode.
For bridge group member interfaces, this implicit permit from a higher to a lower security interface applies to interfaces within the aforementioned span group only. There are no implicit permits betwixt a bridge group member interface and a routed interface or a fellow member of a different bridge group.
Bridge group fellow member interfaces (routed or transparent mode) besides allow the following by default:
-
ARPs in both directions. (You lot tin command ARP traffic using ARP inspection, only yous cannot control it by access rule.)
-
BPDUs in both directions. (You can control these using Ethertype rules.)
For other traffic, you need to apply either an extended admission rule (IPv4 and IPv6) or an EtherType dominion (non-IP).
Implicit Deny
ACLs have an implicit deny at the end of the list, so unless you explicitly allow it, traffic cannot laissez passer. For example, if you desire to allow all users to admission a network through the ASA except for particular addresses, so you demand to deny the particular addresses and then permit all others.
For management (control airplane) ACLs, which control to-the-box traffic, there is no implicit deny at the end of a gear up of management rules for an interface. Instead, whatsoever connexion that does not friction match a management access dominion is and so evaluated by regular access control rules.
For EtherType ACLs, the implicit deny at the end of the ACL does not impact IP traffic or ARPs; for example, if you allow EtherType 8037, the implicit deny at the terminate of the ACL does not now block any IP traffic that you previously allowed with an extended ACL (or implicitly allowed from a high security interface to a low security interface). However, if you explicitly deny all traffic with an EtherType rule, then IP and ARP traffic is denied; only physical protocol traffic, such every bit auto-negotiation, is even so allowed.
If you lot configure a global access rule, then the implicit deny comes afterwards the global rule is processed. See the post-obit order of operations:
-
Interface access dominion.
-
For bridge group fellow member interfaces, the Bridge Virtual Interface (BVI) access rule.
-
Global admission rule.
-
Implicit deny.
NAT and Access Rules
Access rules e'er use the real IP addresses when determining an admission rule lucifer, even if you configure NAT. For case, if you configure NAT for an inside server, 10.ane.i.5, so that information technology has a publicly routable IP address on the outside, 209.165.201.5, then the access rule to permit the outside traffic to access the inside server needs to reference the server'south real IP address (10.1.1.five), and non the mapped address (209.165.201.5).
Same Security Level Interfaces and Admission Rules
Each interface has a security level, and security level checking is performed earlier access rules are considered. Thus, even if you allow a connection in an access rule, it can be blocked due to same-security-level checking at the interface level. You might want to ensure that your configuration allows same-security-level connections so that your access rules are always considered for let/deny decisions.
-
Connections between the same security level ingress and egress interfaces are subject to the same-security-traffic inter-interface check.
To allow these connections, enter the aforementioned-security-traffic permit inter-interface command.
To allow these connections, choose , then select the Enable traffic betwixt two or more interfaces which are configured with the same security levels option.
-
Connections with the same ingress and egress interfaces are subject to the same-security-traffic intra-interface check.
To allow these connections, enter the same-security-traffic permit intra-interface command.
To permit these connections, choose , so select the Enable traffic betwixt two or more than hosts connected to the same interface option.
Extended Access Rules
This section describes data nigh extended access rules.
Extended Admission Rules for Returning Traffic
For TCP, UDP, and SCTP connections for both routed and transparent manner, y'all practise not need an access rule to permit returning traffic because the ASA allows all returning traffic for established, bidirectional connections.
For connectionless protocols such as ICMP, however, the ASA establishes unidirectional sessions, so y'all either demand access rules to allow ICMP in both directions (by applying ACLs to the source and destination interfaces), or you need to enable the ICMP inspection engine. The ICMP inspection engine treats ICMP sessions every bit bidirectional connections. For example, to control ping, specify repeat-respond (0) (ASA to host) or repeat (8) (host to ASA).
Allowing Circulate and Multicast Traffic
In routed firewall mode, circulate and multicast traffic is blocked even if you allow information technology in an access rule, including unsupported dynamic routing protocols and DHCP. Y'all must configure the dynamic routing protocols or DHCP relay to permit this traffic.
For interfaces that are members of the same span group in transparent or routed firewall mode, you can let any IP traffic through using access rules.
 Note | Because these special types of traffic are connectionless, you need to apply an access rule to both the inbound and outbound interfaces, and then returning traffic is immune through. |
The following table lists mutual traffic types that you lot can allow using access rules betwixt interfaces that are members of the same bridge group.
| Traffic Type | Protocol or Port | Notes |
|---|---|---|
| DHCP | UDP ports 67 and 68 | If yous enable the DHCP server, then the ASA does not pass DHCP packets. |
| EIGRP | Protocol 88 | — |
| OSPF | Protocol 89 | — |
| Multicast streams | The UDP ports vary depending on the application. | Multicast streams are e'er destined to a Course D address (224.0.0.0 to 239.x.x.10). |
| RIP (v1 or v2) | UDP port 520 | — |
Direction Admission Rules
Yous tin can configure access rules that control management traffic destined to the ASA. Access control rules for to-the-box management traffic (defined by such commands as http , ssh , or telnet ) have higher precedence than a management access dominion applied with the control-plane option. Therefore, such permitted management traffic volition be allowed to come in fifty-fifty if explicitly denied by the to-the-box ACL.
Unlike regular access rules, there is no implicit deny at the finish of a set of direction rules for an interface. Instead, whatsoever connectedness that does not match a direction access rule is so evaluated by regular access control rules.
Alternatively, y'all can use ICMP rules to command ICMP traffic to the device. Apply regular extended access rules to control ICMP traffic through the device.
EtherType Rules
This section describes EtherType rules.
Supported EtherTypes and Other Traffic
An EtherType rule controls the following:
-
EtherType identified by a 16-bit hexadecimal number, including mutual types IPX and MPLS unicast or multicast.
-
Ethernet V2 frames.
-
BPDUs, which are permitted by default. BPDUs are SNAP-encapsulated, and the ASA is designed to specifically handle BPDUs.
-
Trunk port (Cisco proprietary) BPDUs. Body BPDUs accept VLAN information inside the payload, so the ASA modifies the payload with the outgoing VLAN if yous allow BPDUs.
-
Intermediate System to Intermediate Organization (IS-IS).
-
The IEEE 802.two Logical Link Control packet. You tin command access based on the Destination Service Access Betoken address.
The following types of traffic are not supported:
-
802.3-formatted frames—These frames are not handled by the rule because they use a length field equally opposed to a type field.
EtherType Rules for Returning Traffic
Because EtherTypes are connectionless, y'all need to apply the rule to both interfaces if you want traffic to laissez passer in both directions.
Assuasive MPLS
If y'all allow MPLS, ensure that Characterization Distribution Protocol and Tag Distribution Protocol TCP connections are established through the ASA by configuring both MPLS routers connected to the ASA to employ the IP address on the ASA interface equally the router-id for LDP or TDP sessions. (LDP and TDP allow MPLS routers to negotiate the labels (addresses) used to forward packets.)
On Cisco IOS routers, enter the appropriate command for your protocol, LDP or TDP. The interface is the interface connected to the ASA.
mpls ldp router-id interface strength
Or
tag-switching tdp router-id interface force
Licensing for Access Rules
Admission control rules do not require a special license.
Nevertheless, to utilise sctp every bit the protocol in a rule, you must accept a Carrier license.
Guidelines for Access Control
IPv6 Guidelines
Supports IPv6. The source and destination addresses can include any mix of IPv4 and IPv6 addresses.
Per-User ACL Guidelines
-
The per-user ACL uses the value in the timeout uauth command, merely it can be overridden by the AAA per-user session timeout value.
-
If traffic is denied because of a per-user ACL, syslog bulletin 109025 is logged. If traffic is permitted, no syslog bulletin is generated. The log selection in the per-user ACL has no effect.
Boosted Guidelines and Limitations
-
Over fourth dimension, your list of access rules can grow to include many obsolete rules. Eventually, the ACLs for the access groups can go then big that they impact overall system performance. If you find that the system is having issues sending syslog messages, communicating for failover synchronization, establishing and maintaining SSH/HTTPS management access connections, and and so forth, you might need to clip your access rules. In general, you should actively maintain your dominion lists to remove obsolete rules, rules that are never hit, FQDN objects that can no longer be resolved, and then forth. Also consider implementing object group search.
-
You can reduce the memory required to search access rules by enabling object grouping search, only this is at the expense rule of lookup performance and increased CPU utilization. When enabled, object group search does not expand network or service objects, but instead searches access rules for matches based on those group definitions. You tin set this option using the object-group-search access-control command.
You tin can apply the object-group-search threshold command to enable a threshold to assistance foreclose performance degradation. When operating with a threshold, for each connection, both the source and destination IP addresses are matched against network objects. If the number of objects matched by the source accost times the number matched by the destination address exceeds 10,000, the connection is dropped. Configure your rules to prevent an excessive number of matches.

Note
Object group search works with network and service objects only. It does not piece of work with security grouping or user objects. Practise non enable this feature if the ACLs include security groups. The upshot can exist inactive ACLs or other unexpected behavior.
-
Yous tin can better system performance and reliability by using the transactional commit model for access groups. Run across the basic settings affiliate in the general operations configuration guide for more than information. Use the asp rule-engine transactional-commit admission-group command.
-
In ASDM, rule descriptions are based on the access listing remarks that come before the rule in the ACL; for new rules you create in ASDM, any descriptions are besides configured every bit remarks earlier the related rule. However, the packet tracer in ASDM matches the remark that is configured after the matching dominion in the CLI.
-
Commonly, you cannot reference an object or object group that does non exist in an ACL or object group, or delete one that is currently referenced. You besides cannot reference an ACL that does not be in an access-group command (to apply access rules). Even so, you tin can change this default behavior so that y'all can "forward reference" objects or ACLs before you create them. Until y'all create the objects or ACLs, any rules or access groups that reference them are ignored. To enable forward referencing, use the forward-reference enable command.
Configure Access Control
The following topics explain how to configure access control.
Configure an Access Group
Before you tin create an admission grouping, create the ACL.
To bind an ACL to an interface or to apply information technology globally, apply the following control:
admission-group access_list { {in| out} interface interface_name [per-user-override | control-plane] | global}
For an interface-specific access group:
-
Specify the extended or EtherType ACL name. Yous tin can configure one admission-group command per ACL type per interface per direction, and ane control plane ACL. The control aeroplane ACL must exist an extended ACL. Ethertype ACLs are allowed on bridge group member interfaces simply. For span groups in routed way, you tin specify extended ACLs for each direction on both the Bridge Virtual Interface (BVI) and each span group member interface.
-
The in keyword applies the ACL to inbound traffic. The out keyword applies the ACL to the outbound traffic.
-
Specify the interface proper noun.
-
The per-user-override keyword (for inbound extended ACLs only) allows dynamic user ACLs that are downloaded for user authorization to override the ACL assigned to the interface. For example, if the interface ACL denies all traffic from 10.0.0.0, simply the dynamic ACL permits all traffic from 10.0.0.0, then the dynamic ACL overrides the interface ACL for that user.
By default, VPN remote access traffic is not matched against interface ACLs. However, if you utilize the no sysopt connexion let-vpn command to turn off this bypass, the behavior depends on whether there is a vpn-filter practical in the group policy and whether you fix the per-user-override option:
-
No per-user-override, no vpn-filter—Traffic is matched confronting the interface ACL.
-
No per-user-override, vpn-filter—Traffic is matched beginning against the interface ACL, then confronting the VPN filter.
-
per-user-override, vpn-filter—Traffic is matched against the VPN filter just.
-
-
The control-plane keyword specifies if the extended ACL is for to-the-box traffic.
Unlike regular access rules, at that place is no implicit deny at the end of a set up of management (control plane) rules for an interface. Instead, any connectedness that does not match a management access rule is then evaluated past regular access control rules.
For a global access group, specify the global keyword to apply the extended ACL to the inbound direction of all interfaces.
Instance
The following example shows how to use the access-group control:
hostname(config)# admission-list outside_access allow tcp any host 209.165.201.3 eq lxxx hostname(config)# access-group outside_access in interface outside The access-list control lets whatsoever host access the host address using port 80. The access-grouping control specifies that the admission-list command applies to traffic entering the outside interface.
Configure ICMP Access Rules
By default, y'all can send ICMP packets to any interface using either IPv4 or IPv6, with these exceptions:
-
The ASA does not reply to ICMP echo requests directed to a broadcast accost.
-
The ASA only responds to ICMP traffic sent to the interface that traffic comes in on; y'all cannot send ICMP traffic through an interface to a far interface.
To protect the device from attacks, you lot can use ICMP rules to limit ICMP access to interfaces to particular hosts, networks, or ICMP types. ICMP rules function like access rules, where the rules are ordered, and the first rule that matches a packet defines the action.
If y'all configure whatever ICMP dominion for an interface, an implicit deny ICMP dominion is added to the end of the ICMP rule list, irresolute the default behavior. Thus, if y'all desire to just deny a few bulletin types, you must include a let any rule at the end of the ICMP rule listing to let the remaining bulletin types.
We recommend that yous ever grant permission for the ICMP unreachable message blazon (type three). Denying ICMP unreachable letters disables ICMP path MTU discovery, which can halt IPsec and PPTP traffic. Additionally ICMP packets in IPv6 are used in the IPv6 neighbor discovery process.
Procedure
| Step ane | Create rules for ICMP traffic. icmp {permit | deny} {host ip_address | ip_address mask | whatever} [icmp_type] interface_name If yous exercise not specify an icmp_type, the rule applies to all types. You can enter the number or the proper name. To command ping, specify echo-reply (0) (ASA-to-host) or echo (8) (host-to-ASA). For the address, yous can apply the rule to any address, to a single host, or to a network (ip_address mask). |
| Footstep 2 | Create rules for ICMPv6 (IPv6) traffic. ipv6 icmp {permit | deny} {host ipv6_address | ipv6-network/prefix-length | whatsoever} [icmp_type] interface_name If you do non specify an icmp_type, the rule applies to all types. For the address, y'all can utilise the dominion to whatsoever address, to a single host, or to a network (ipv6-network/prefix-length). |
| Step 3 | (Optional.) Set charge per unit limits on ICMP Unreachable messages then that the ASA volition announced on trace route output. icmp unreachable rate-limit charge per unit burst-size size The charge per unit limit tin be ane-100, with 1 existence the default. The flare-up size is meaningless, but must exist i-x. Case:Increasing the rate limit, along with enabling the gear up connectedness decrement-ttl control in a service policy, is required to allow a traceroute through the ASA that shows the ASA as one of the hops. For example, the post-obit policy increases the rate limit and decrements the time-to-live (TTL) value for all traffic through the ASA. |
Examples
The post-obit example shows how to allow all hosts except the one at 10.ane.one.15 to utilize ICMP to the inside interface:
hostname(config)# icmp deny host 10.1.1.15 inside hostname(config)# icmp permit whatever within The following example shows how to allow the host at x.1.1.15 to use only ping to the inside interface:
hostname(config)# icmp permit host 10.1.one.15 inside The following example shows how to deny all ping requests and permit all parcel-too-large messages (to support path MTU discovery) at the outside interface:
hostname(config)# ipv6 icmp deny whatever repeat-reply outside hostname(config)# ipv6 icmp permit any packet-too-big outside The following case shows how to allow host 2000:0:0:4::2 or hosts on prefix 2001::/64 to ping the exterior interface:
hostname(config)# ipv6 icmp permit host 2000:0:0:4::ii repeat-answer outside hostname(config)# ipv6 icmp permit 2001::/64 echo-reply exterior hostname(config)# ipv6 icmp permit any packet-too-big outside Monitoring Access Rules
To monitor network admission, enter the following commands:
-
clear access-list id counters
Articulate the hit counts for the access list.
-
show access-list [proper noun]
Displays the access lists, including the line number for each ACE and hit counts. Include an ACL name or you will encounter all access lists.
-
bear witness running-config access-group
Displays the electric current ACL bound to the interfaces.
Evaluating Syslog Letters for Access Rules
Utilise a syslog consequence viewer, such as the one in ASDM, to view messages related to access rules.
If yous use default logging, you meet syslog bulletin 106023 for explicitly denied flows only. Traffic that matches the "implicit deny" entry that ends the dominion listing is not logged.
If the ASA is attacked, the number of syslog messages for denied packets can exist very large. We recommend that you instead enable logging using syslog bulletin 106100, which provides statistics for each dominion (including allow rules) and enables you lot to limit the number of syslog messages produced. Alternatively, you lot can disable all logging for a given dominion.
When you enable logging for bulletin 106100, if a packet matches an ACE, the ASA creates a flow entry to track the number of packets received within a specific interval. The ASA generates a syslog message at the commencement hit and at the end of each interval, identifying the total number of hits during the interval and the time postage for the last hit. At the terminate of each interval, the ASA resets the striking count to 0. If no packets match the ACE during an interval, the ASA deletes the flow entry. When you configure logging for a rule, you can command the interval and even the severity level of the log message, per dominion.
A flow is defined by the source and destination IP addresses, protocols, and ports. Because the source port might differ for a new connection between the aforementioned two hosts, you might not come across the same flow increment because a new menstruum was created for the connection.
Permitted packets that vest to established connections do not demand to exist checked against ACLs; only the initial packet is logged and included in the hitting count. For connectionless protocols, such as ICMP, all packets are logged, even if they are permitted, and all denied packets are logged.
See the syslog letters guide for detailed information about these letters.
 Tip | When you enable logging for message 106100, if a package matches an ACE, the ASA creates a flow entry to rail the number of packets received within a specific interval. The ASA has a maximum of 32 One thousand logging flows for ACEs. A large number of flows can exist concurrently at any point of time. To foreclose unlimited consumption of retentiveness and CPU resources, the ASA places a limit on the number of concurrent deny flows; the limit is placed on deny flows just (non on let flows) because they can betoken an attack. When the limit is reached, the ASA does not create a new deny menses for logging until the existing flows expire, and issues bulletin 106101. Y'all can control the frequency of this message using the access-list alert-interval secs command, and the maximum number of deny flows cached using the access-list deny-flow-max number command. |
Configuration Examples for Permitting or Denying Network Access
Following are some typical configuration examples for permitting or denying network access.
Extended ACL Examples
The post-obit example adds a network object for inside server i, performs static NAT for the server, and enables admission from the outside for inside server 1.
hostname(config)# object network inside-server1 hostname(config)# host 10.1.one.1 hostname(config)# nat (inside,outside) static 209.165.201.12 hostname(config)# admission-listing outside_access extended allow tcp any object inside-server1 eq www hostname(config)# access-grouping outside_access in interface outside The following example allows all hosts to communicate between the inside and hr networks but only specific hosts to admission the outside network:
hostname(config)# access-list ANY extended permit ip whatever any hostname(config)# access-list OUT extended permit ip host 209.168.200.3 whatever hostname(config)# access-list OUT extended allow ip host 209.168.200.four any hostname(config)# admission-group Whatever in interface within hostname(config)# access-group Whatsoever in interface hr hostname(config)# access-grouping OUT out interface outside The following example uses object groups to permit specific traffic on the inside interface:
! hostname (config)# object-group service myaclog hostname (config-service)# service-object tcp source range 2000 3000 hostname (config-service)# service-object tcp source range 3000 3010 destinatio$ hostname (config-service)# service-object ipsec hostname (config-service)# service-object udp destination range 1002 1006 hostname (config-service)# service-object icmp echo hostname(config)# access-list outsideacl extended allow object-group myaclog interface inside whatsoever EtherType Examples
For instance, the following sample ACL allows common EtherTypes originating on the within interface:
hostname(config)# admission-listing ETHER ethertype permit ipx INFO: ethertype ipx is saved to config equally ethertype eii-ipx INFO: ethertype ipx is saved to config as ethertype dsap ipx INFO: ethertype ipx is saved to config as ethertype dsap raw-ipx hostname(config)# access-list ETHER ethertype permit mpls-unicast hostname(config)# access-group ETHER in interface inside The following example allows some EtherTypes through the ASA, but it denies all others:
hostname(config)# access-list ETHER ethertype permit 0x1234 hostname(config)# admission-list ETHER ethertype permit mpls-unicast hostname(config)# access-group ETHER in interface inside hostname(config)# access-grouping ETHER in interface outside The following example denies traffic with EtherType 0x1256 only allows all others on both interfaces:
hostname(config)# access-list nonIP ethertype deny 1256 hostname(config)# admission-listing nonIP ethertype permit any hostname(config)# access-grouping nonIP in interface inside hostname(config)# access-group nonIP in interface outside History for Admission Rules
| Feature Proper noun | Platform Releases | Description |
|---|---|---|
| Interface access rules | 7.0(i) | Controlling network access through the ASA using ACLs. We introduced the following command: access-group. |
| Global access rules | 8.3(one) | Global access rules were introduced. Nosotros modified the following control: access-group. |
| Support for Identity Firewall | 8.4(2) | You can now use identity firewall users and groups for the source and destination. Y'all can use an identity firewall ACL with admission rules, AAA rules, and for VPN authentication. We modified the post-obit commands: access-list extended . |
| EtherType ACL support for IS-IS traffic | 8.4(5), ix.ane(2) | In transparent firewall fashion, the ASA tin now pass IS-IS traffic using an EtherType ACL. We modified the following command: access-listing ethertype {permit | deny} isis. |
| Back up for TrustSec | 9.0(ane) | You can now employ TrustSec security groups for the source and destination. You tin can use an identity firewall ACL with admission rules. We modified the post-obit commands: access-list extended . |
| Unified ACL for IPv4 and IPv6 | 9.0(one) | ACLs at present support IPv4 and IPv6 addresses. You can even specify a mix of IPv4 and IPv6 addresses for the source and destination. The whatever keyword was inverse to stand for IPv4 and IPv6 traffic. The any4 and any6 keywords were added to correspond IPv4-only and IPv6-only traffic, respectively. The IPv6-specific ACLs are deprecated. Existing IPv6 ACLs are migrated to extended ACLs. Run into the release notes for more information about migration. We modified the following commands: access-list extended , access-list webtype . We removed the following commands: ipv6 access-list, ipv6 access-list webtype, ipv6-vpn-filter |
| Extended ACL and object enhancement to filter ICMP traffic by ICMP lawmaking | 9.0(1) | ICMP traffic can now be permitted/denied based on ICMP lawmaking. We introduced or modified the following commands: access-list extended , service-object, service. |
| Transactional Commit Model on Access Group Rule Engine | 9.one(5) | When enabled, a dominion update is applied after the rule compilation is completed; without affecting the dominion matching operation. We introduced the post-obit commands: asp dominion-engine transactional-commit, bear witness running-config asp dominion-engine transactional-commit, clear configure asp rule-engine transactional-commit. |
| Configuration session for editing ACLs and objects. Frontward referencing of objects and ACLs in access rules. | 9.3(2) | You tin now edit ACLs and objects in an isolated configuration session. You can also forrad reference objects and ACLs, that is, configure rules and access groups for objects or ACLs that do non yet exist. Nosotros introduced the clear config-session, articulate session, configure session, forrard-reference, and prove config-session commands. |
| Admission rule back up for Stream Command Manual Protocol (SCTP) | 9.5(2) | You can now create access rules using the sctp protocol, including port specifications. We modified the following control: access-list extended . |
| Ethertype rule support for the IEEE 802.2 Logical Link Control parcel'south Destination Service Access Point address. | 9.6(two) | You tin can now write Ethertype admission command rules for the IEEE 802.2 Logical Link Command bundle'south Destination Service Access Betoken address. Because of this addition, the bpdu keyword no longer matches the intended traffic. Rewrite bpdu rules for dsap 0x42 . We modified the following commands: access-list ethertype |
| Back up in routed mode for Ethertype rules on bridge group member interfaces and extended access rules on Span Grouping Virtual Interfaces (BVI). | 9.7(1) | You tin now create Ethertype ACLs and use them to bridge grouping member interfaces in routed manner. You can also employ extended access rules to the Bridge Virtual Interface (BVI) in add-on to the member interfaces. Nosotros modified the following commands: access-group , access-listing ethertype . |
| EtherType access control list changes. | 9.9(1) | EtherType access control lists now support Ethernet Two IPX (EII IPX). In addition, new keywords are added to the DSAP keyword to support common DSAP values: BPDU (0x42), IPX (0xE0), Raw IPX (0xFF), and ISIS (0xFE). Consequently, existing EtherType admission control entries that use the BPDU or ISIS keywords will be converted automatically to use the DSAP specification, and rules for IPX will exist converted to 3 rules (DSAP IPX, DSAP Raw IPX, and EII IPX). In add-on, packet capture that uses IPX as an EtherType value has been deprecated, because IPX corresponds to 3 separate EtherTypes. We modified the following commands: access-list ethertype added the new keywords eii-ipx and dsap {bpdu | ipx | isis | raw-ipx} ; capture ethernet-type no longer supports the ipx keyword. |
| The object group search threshold is now disabled by default. | 9.12(1) | If you enabled object group search, the feature was discipline to a threshold to help preclude performance degradation. That threshold is now disabled past default. You can enable it by using the object-group-search threshold command. We added the following command: object-group-search threshold . |
Which Of These Would Not Be A Filtering Mechanism Found In A Firewall Acl Rule?,
Source: https://www.cisco.com/c/en/us/td/docs/security/asa/asa914/configuration/firewall/asa-914-firewall-config/access-rules.html
Posted by: georgeimettences.blogspot.com


0 Response to "Which Of These Would Not Be A Filtering Mechanism Found In A Firewall Acl Rule?"
Post a Comment